RCDF: A maturity model for machine-speed cyber defense
RCDF (Recursive Cyber Defense Framework) is a defense maturity framework designed to measure and improve an organization’s ability to detect, decide, and intervene at machine-speed without sacrificing governance and control.
.svg)
.svg)
Why RCDF Exists
Modern cyber attacks now operate at machine speed. Automated execution, AI-driven adaptation, and compressed attack cycles allow adversaries to detect, decide, and act in milliseconds.
Most defensive programs, however, are still measured and operated at human speed. Detection may be automated, but decisions and actions remain gated by manual review, coordination across teams, and sequential approval steps.
Existing security frameworks were designed under an assumption that time is available to analyze, to escalate, and to intervene. That assumption no longer holds.
The problem is not tooling.
The problem is latency.

The Human Latency Wall
Human decision-making has a hard lower bound. Below a certain threshold, people cannot reliably observe, decide, and act. Modern cyber attacks now operate beyond that limit.
Human response is unreliable below ~250 milliseconds.
Modern attacks routinely operate below this threshold.
Defensive actions below this boundary must be machine-executed.
Human intervention at this speed introduces delay.


Why Existing Frameworks Break
Frameworks such as NIST CSF and ISO 27001 are highly effective at measuring control coverage, policy maturity, and governance alignment. However, they were not designed to assess whether defenses can operate fast enough to survive autonomous, adaptive attacks. RCDF does not replace these frameworks. It addresses a different question: not whether controls exist, but whether the system can survive contact with a machine-speed adversary.
.webp)


What RCDF Focuses On
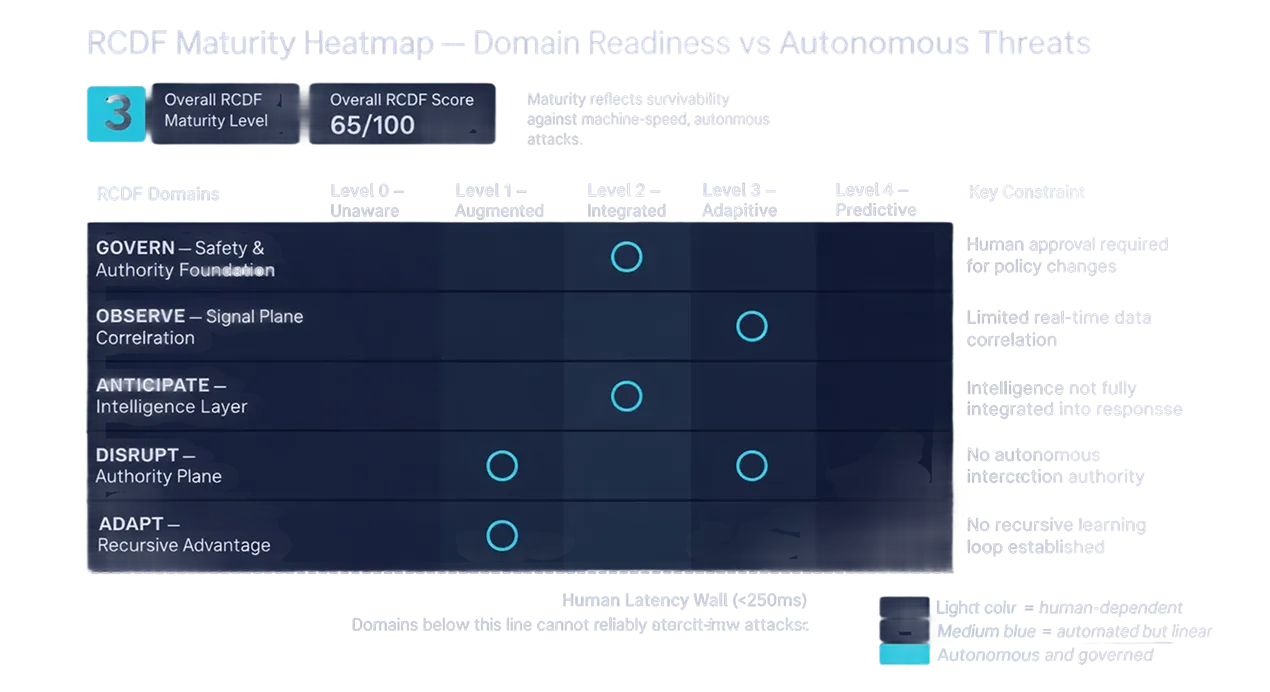
RCDF evaluates five core domains that together determine whether autonomous cyber defense is possible. These domains operate continuously and concurrently; they are not stages or steps.
Each domain represents a non-negotiable capability area required to perceive threats, infer intent, interdict attacks, and improve after contact.
Policy & Authority
Signal & Visibility
Prediction & Intelligence
Prohibition & Control
Learning & Adaptation


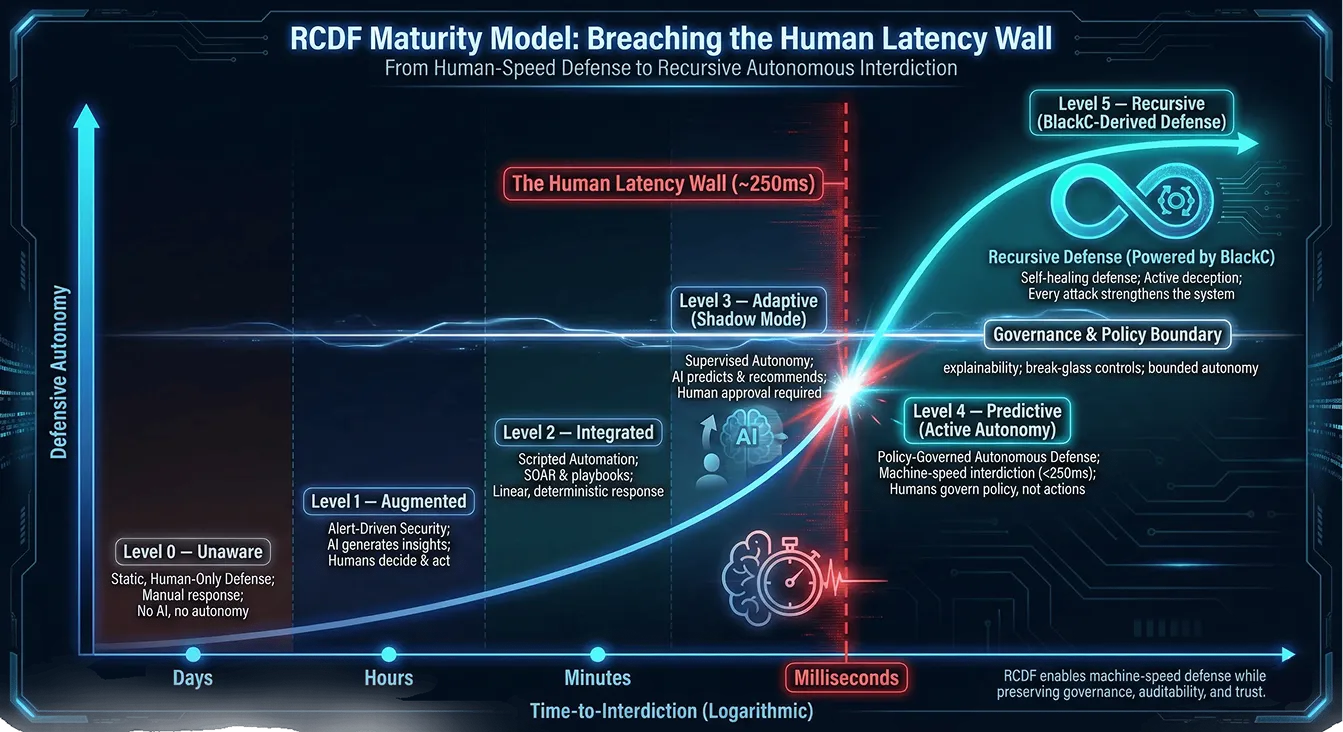
The RCDF Maturity Model
The RCDF maturity model describes how organizations progress from human-speed, reactive defense toward governed, recursive autonomy. Lower maturity levels depend heavily on manual decision-making and linear automation. Higher levels demonstrate machine-speed execution under enforced policy and continuous improvement.
Breaching the Human Latency Wall requires autonomy, but autonomy that is bounded, auditable, and revocable.

Use Cases RCDF Addresses

Adversarial Use Cases
RCDF is designed to model modern adversarial behavior, including autonomous lateral movement, adaptive evasion of static controls, and attacks intended to overwhelm or corrupt defensive signals and human decision-making.

Defensive Use Cases
RCDF enables the design and assessment of AI-native security operations, autonomous interdiction under governance, and executive-level visibility into cyber survivability — translating technical capability into decision-grade insight.

How the RCDF Assessment Works
RCDF assessments are function-based and evidence-driven. They evaluate how the system actually behaves under realistic conditions, not how it is intended to behave. The assessment examines diagnostic capabilities across all RCDF domains, measures maturity using objective evidence, analyzes latency and autonomy boundaries, and identifies survivability gaps that materially affect defense outcomes.
%2C%20354856.%200A1119%20-%20bg%20color%2C%20no%20scale%201.webp)

What You Get
An RCDF assessment produces decision artifacts designed for both technical and executive audiences. Outputs include a maturity scorecard, a control effectiveness rubric, and heatmaps that clearly show strengths, weaknesses, and risk concentration.
Detailed findings translate directly into architectural and operational recommendations.
.webp)


RCDF as a
Living Framework
RCDF is designed to remain structurally relevant as threats evolve. It underpins assessment, architecture, and execution providing a durable foundation for autonomous cyber defense rather than a static checklist.
Its purpose is not compliance, but survivability.
Download the
RCDF Whitepaper
RCDF Documentation
A structured overview of the Recursive Cyber Defense Framework, including core concepts, maturity model, and assessment methodology.
Request an RCDF assessment to identify gaps and plan improvements.
