What BlackC Micro Products Are
BlackC micro products are small, purpose-built capability units designed to operate within the BlackC dual-mode neural network. Each micro product delivers a narrowly scoped function such as simulation, analysis, or controlled response, while relying on BlackC for coordination, governance, and policy enforcement.
Micro products are not deployed or operated independently. They are activated, constrained, and validated by the BlackC.
.svg)
.svg)
Why Micro Products Exist
— Villages, Not Cities
Traditional security platforms resemble cities: large, tightly coupled, and difficult to change without introducing systemic risk. When a city fails, the blast radius is wide and recovery is slow.
BlackC micro products are designed as villages.
01
Why villages instead of cities
Smaller scope reduces blast radius and failure impact
Capabilities can evolve independently without destabilizing the system
Governance and control are easier to enforce and audit
New villages can be added without redesigning the entire environment
02
How villages are assembled
Just as real villages are built around essential services — fire, police, hospitals, schools — BlackC micro products are assembled from preconfigured critical technology services, rather than custombuilt each time.
03
Examples of preconfigured services
Identity and access control (IAM)
Data security and classification
Network security and segmentation
Telemetry, logging, and evidence capture
Policy enforcement and authorization
These services are predesigned to operate safely within both modes of the BlackC dual-mode neural network, enabling faster deployment with lower risk.

.png)
How Micro Products
Relate to the BlackC
The BlackC provides the coordination and governance layer for all micro products. It determines when a micro product is invoked, what authority it has, what data it can access, and how its outputs are used.
Micro products communicate through the BlackC rather than directly with each other, ensuring consistent policy enforcement and auditability.
Micro Product Use Case Overview
The following are usecase placeholders, not deployed products. Images are used to illustrate capability areas rather than specific implementations.

Non-Human Identity Takeover Interdiction: Token Abuse Detected by Sequence and Velocity
.svg)
Staging / Pre-Production Enviroment (Controlled)
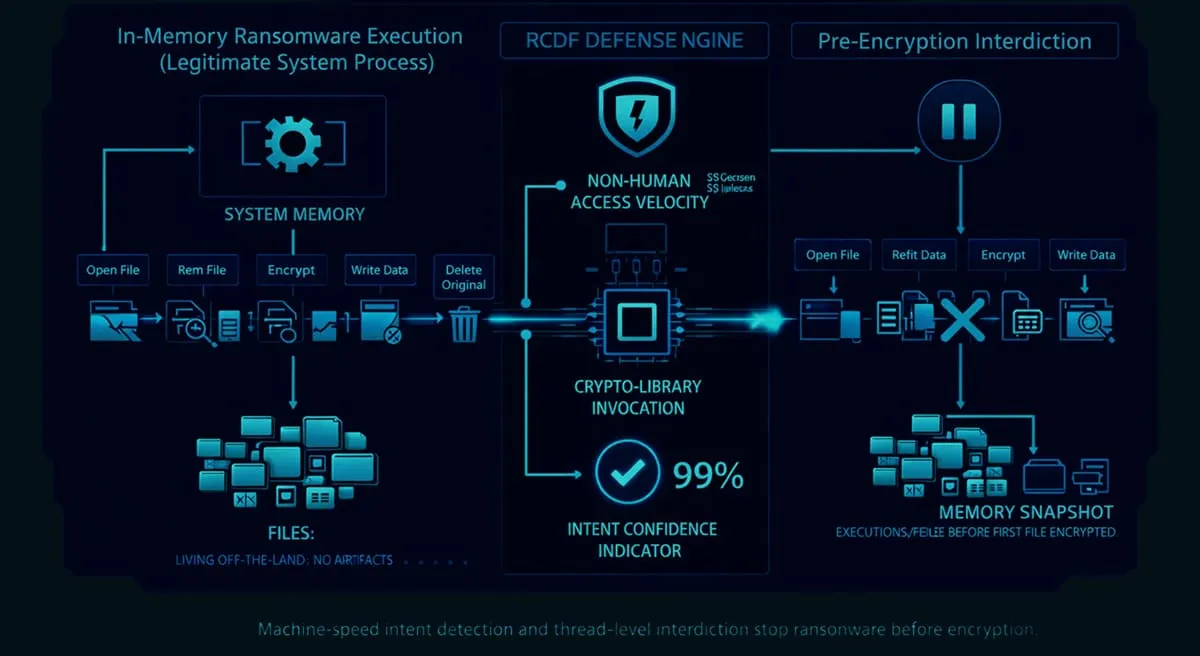
In-Memory Ransomware Execution (Legitimate System Process)
.svg)
Testing AI systems for behavioral abuse and evasion through controlled; black-box interaction

Governance
and Safety Model
Micro products inherit governance from the BlackC. They cannot exceed the authority granted to them, operate outside defined scope, or bypass policy enforcement.
All actions performed by micro products remain bounded, attributable, and reviewable within the BlackC dual-mode architecture.

Composability
and Evolution
New micro products can be introduced without redesigning existing workflows. Capabilities can be composed, replaced, or retired as threats evolve while BlackC preserves continuity, governance, and operational context.
This allows the system to evolve without accumulating uncontrolled complexity.

How it Fits with RCDF
RCDF assessments identify capability gaps and maturity constraints. BlackC determines how those gaps should be addressed operationally.
Micro products provide the targeted capabilities used to close those gaps under the control and validation mechanisms defined by RCDF and enforced by BlackC.

Capabilities,
Not Tools
BlackC micro products are not standalone tools or platforms. They are governed capability components designed to operate as part of a larger autonomous defense system.
Their value lies in how they are coordinated, constrained, and validated not in isolation.

Fill out the form and our team will respond within 2 business days. You can include any questions or context to help us understand your needs.
