BlackC: the orchestration engine for governed, machine-speed defense
BlackC coordinates defensive workflows across tools, agents, and modular capability “islands” with policy and audit guardrails to keep actions controlled and reviewable.
Talk to BlackC Studio
.svg)
.svg)
What BlackC Is
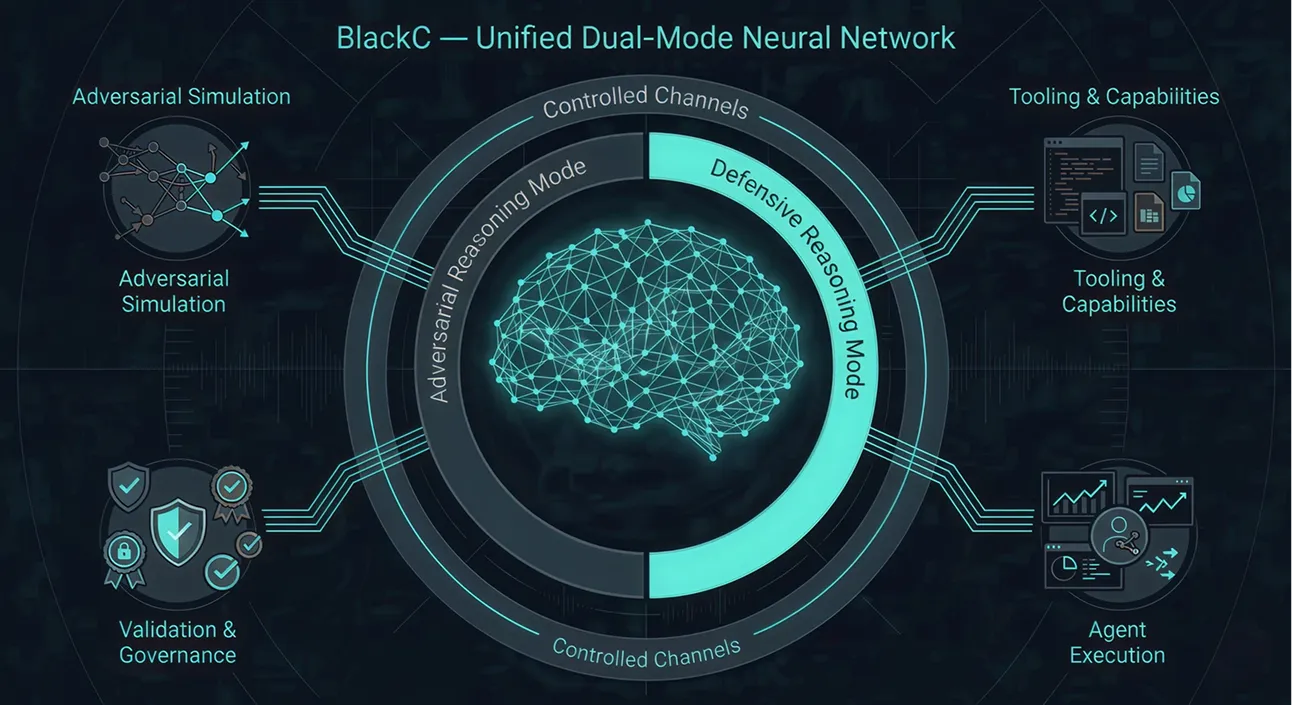
BlackC is the control and coordination layer that enables governed cyber defense at machine speed. It provides a single orchestration point to sequence detection, decision, and action across existing security tools and modular capability components while enforcing policy boundaries and producing reviewable evidence.
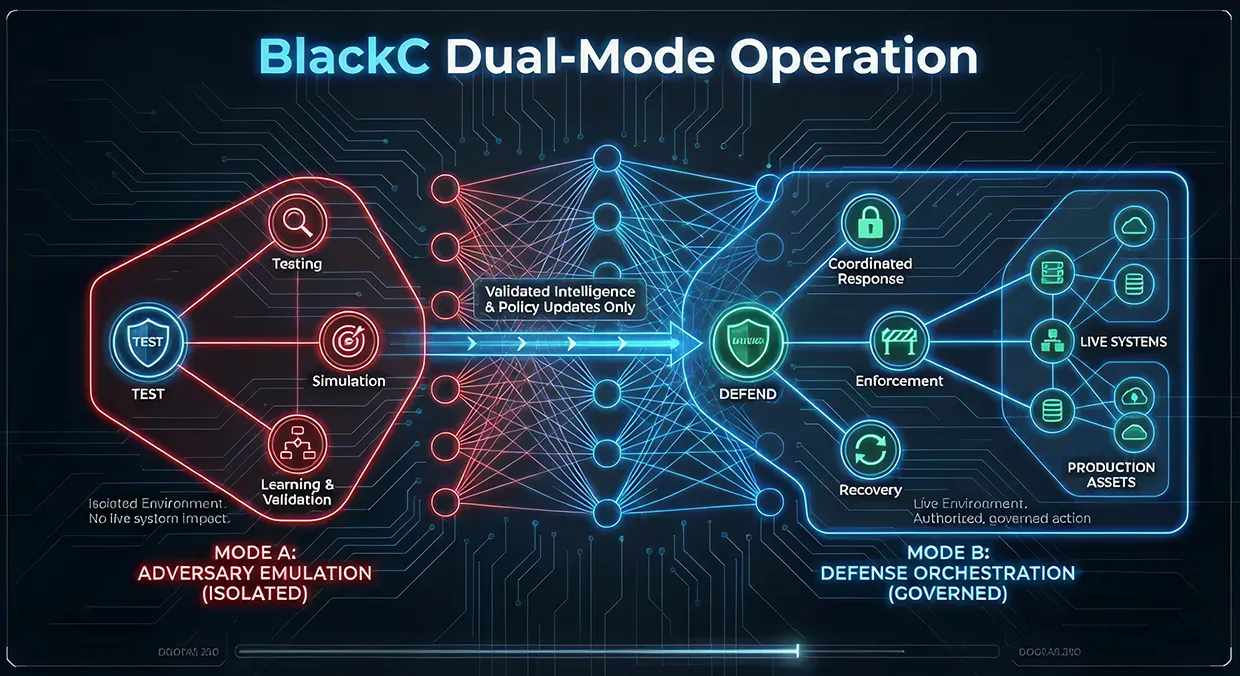
BlackC is built around a dual-mode operating concept: controlled adversary emulation for validation, and defense orchestration for governed response.

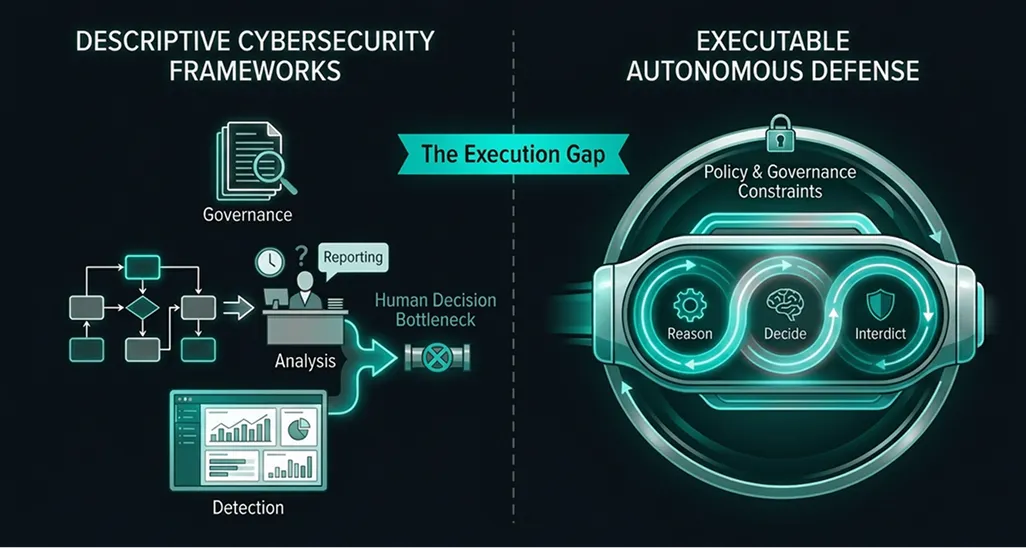
The Execution Gap
Most security programs fail not at detection, but at execution. Decisions arrive too late, actions are manually constrained, or automation cannot be trusted to operate safely at scale.
BlackC was created to close this execution gap, enabling machine-speed action without sacrificing governance, safety, or accountability.

What BlackC Does
Workflow Orchestration
Orchestrates detection → decision → action workflows across tools and teams.
Agent Coordination
Coordinates specialized agents and toolchains under customer-defined authorization boundaries.
Context Management
Maintains operational context (environment state, telemetry signals, and outcomes).
Governance Enforcement
Enforces governance: scope constraints, approvals (as configured), and evidence logging.
Modular Integration
Standardizes how modular capability components integrate with the core system.
Mode A: Adversary Emulation — controlled testing and rehearsal to validate defenses and expose gaps.
Mode B: Defense Orchestration — governed actions to contain, mitigate, and recover within defined authorization boundaries.
Modes can be configured for learning or operational response depending on policy and authorization constraints.


How It Fits Together
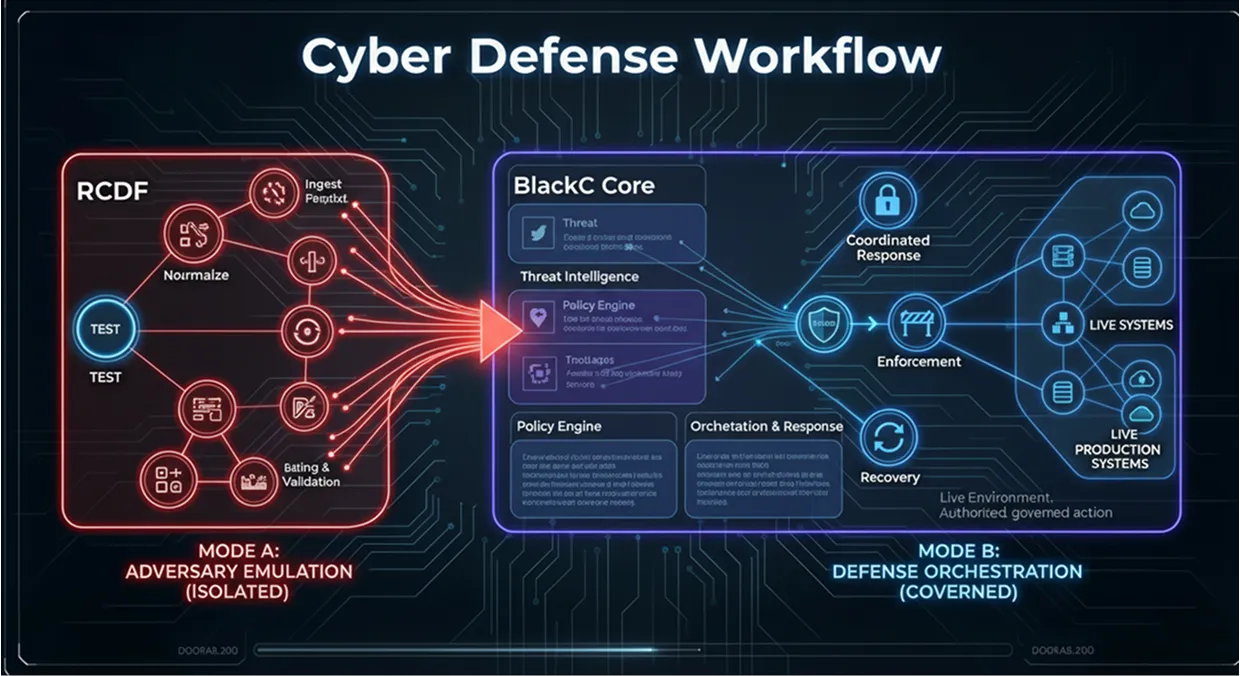
RCDF defines the diagnostic structure for autonomous cyber defense: what must be measured, what maturity looks like, and where survivability gaps exist. BlackC is the operational counterpart. RCDF assessments determine what must change.
BlackC provides the governed neural execution environment to enact, validate, and enforce those changes. Micro products are the applied capability units within that environment. Designed and assembled around specific defensive or adversarial objectives, they operate inside BlackC’s bounded architecture inheriting its isolation, governance, and dual-mode reasoning. Together: RCDF diagnoses, BlackC orchestrates, Micro products execute.
Fill out the form and our team will respond within 2 business days. You can include any questions or context to help us understand your needs.
